KVM allows for the computers themselves to be relocated to a cloud or climate-controlled environment where they're free from noise, excessive heat, dust, etc.; also where they are more easily accessible by IT professionals.
 Keyboard-Video-Mouse, or KVM "¦ Where Information Technology Meets Operational Technology
Keyboard-Video-Mouse, or KVM "¦ Where Information Technology Meets Operational Technology

Q&A with Don Hosmer, VP Sales Americas & General Manager | G&D North America Inc.
1. What is KVM and how does today's technology differ from what was initially introduced decades ago?
Keyboard, video and mouse, or KVM, refers to the respective interfaces of a computer. KVM technology supports Industry 4.0. While it has been used in industrial automation for decades, the more current trend of increased deployment of computer systems and IT-based processes has created an increased need for ideal, and a more flexible, system access. That’s where cutting-edge technologies like KVM come into play.
KVM allows you to separate man and machine by removing the physical computer from the workplace, but maintaining the interface and access to real-time data. The second advantage is the increased flexibility KVM provides. It allows an operator to handle several processes at a time. Each console can show a number of screens, and each screen can show individual computer sources so the operator can survey and operate all those machines at one time. KVM allows you to have the right system available at the right time. It’s for seamless switching between computers or for handling huge consoles with many, many screens with just a single keyboard and mouse.
2. What are some of the motivations behind separating man from machine? Why is that important?
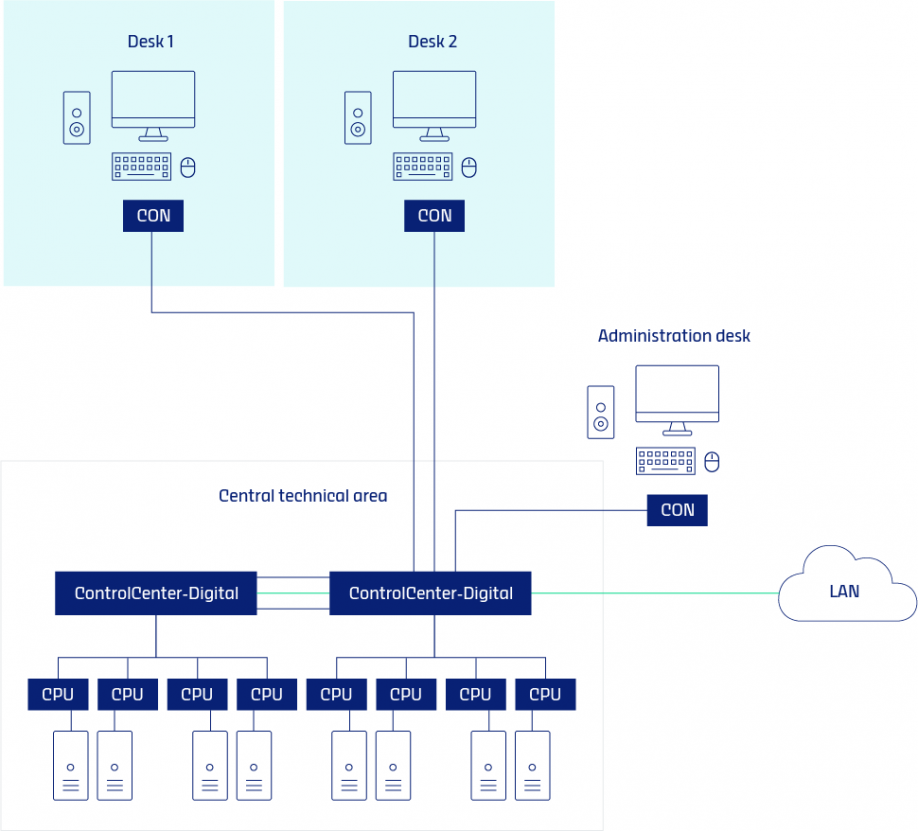
We’re not taking away an operator’s interface or access to critical data. Rather, KVM allows for the computers themselves to be relocated to a cloud or climate-controlled environment where they’re free from noise, excessive heat, dust, etc.; also where they are more easily accessible by IT professionals. All the while, data is still accessible, and latency-free, to operators regardless of their location, whether they’re on a production floor of a factory, a command center, or miles offshore on an oil rig.
3. What are some specific, functional components of KVM that are part of a common installation?
A sampling of the more common KVM applications in process automation settings include:
-
Cross-display switching. Here, the operator has virtually any number of screens they must monitor, each showing an individual computer. KVM technology allows operation of all the different screens/computers with one keyboard and mouse. With cross-display switching, moving the mouse to the screen border can intuitively trigger the KVM system to realize the operator wants to move over to the process on that next screen. In that moment, the KVM system automatically switches the operational focus to that neighboring screen and the neighboring computer.
-
Scenario switching. This is another intuitive function where switching conditions are stored in one or more workplaces – or the entire system – and can be accessed and executed through the on-screen display of workplaces assigned with the required rights. We see this in practice in scenarios where a workplace needs to quickly switch from “normal” mode to “emergency” mode, or from day to night shift for specific tasks, for example.
-
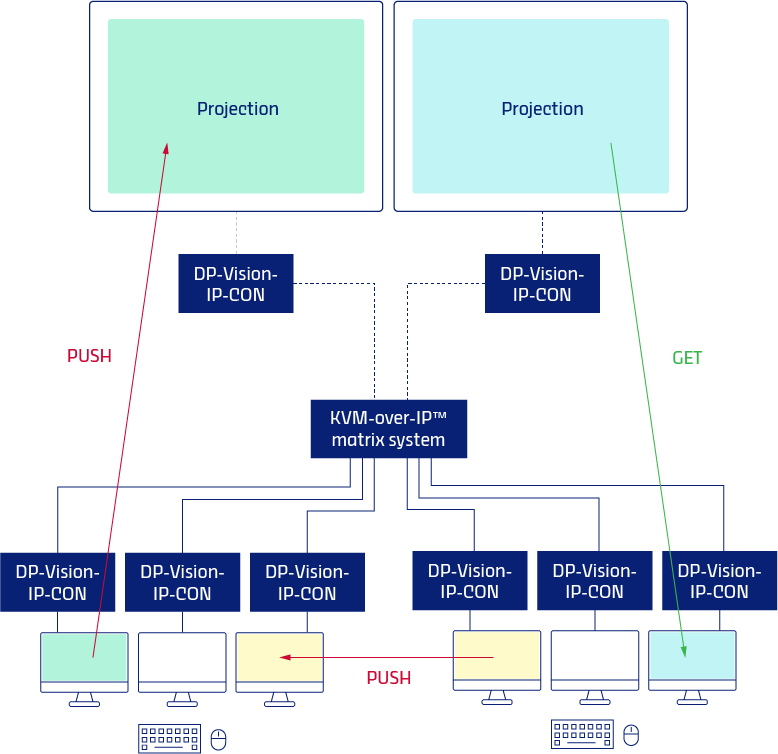
Push-get. This function allows a user, for example in a collaboration or control room context, to “push” their screen to the console of a neighbor or colleague. In a control room, the operator can push what they’re seeing on their screen to the big screen in the room for others to see, for instance. This function is particularly useful during an incident when a colleague may have specific expertise that is needed for a critical task.
-
-
IP Control API. This tool enables controlling of the KVM system from outside via external commands or external devices, and to integrate the KVM with surrounding technology. With this function, an operator can send switching commands to the central module, and the commands are sent via the network. The system can be operated independently from user modules.
-
Hybrid infrastructure. This refers to connecting infrastructure when some computers are on-premises and others are in the cloud. It’s an industry standard and a necessity in most installations today.
4. Describe a recent installation and how it benefited an organization.
KVM was a welcome addition to an oil and gas rig application in the North Sea, both from a data access and employee safety perspective. Oil rigs can be more than 60 miles off the mainland. Further, conditions on the ships and on the floating or fixed platforms can be rough and dangerous. That’s why this particular organization relocated its monitoring function to the mainland for the safety of its employees.
Through a complex KVM install, the former “classic” control room was reimagined to become a flexible “multi-purpose collaboration and interaction center” that completely digitized the interactions between staff at sea and staff on land – with KVM playing a central role.
KVM solutions enabled remote operation of all computers located in access-secured server rooms without any latency and in real time from the control center. Here, the video feeds of the pre-installed surveillance cameras on the drilling rigs run together and can be flexibly switched on the controller workplaces as well as on video walls. All processes shown on the huge displays, projection screens and canvases in meeting and control rooms are supported by KVM systems.
Altogether, 13 different systems were included in the KVM infrastructure. The demands on the systems are extremely high, as they must enable maximum availability, fail-safety and redundancy. All of these aspects are covered by VLAN and routed networks. The system architecture is based on several independent VLANs. This means that operators from the individual control rooms are not permitted to access the servers of the adjacent control rooms or to see them at all.
This KVM install not only future-proofed business operations, but it improved employee safety and comfort, and increased the efficiency of all integrated processes. The organization involved plans to install similar systems in other locations.
5. Discuss how cybersecurity plays into a KVM installation. How does an organization guard against introducing cyber security risks when allowing the kind of remote access we're talking about here?
Removing the computer from the desk is a core strategy for protecting its access. For starters, it eliminates the common types of internal cyberattacks involving individuals – either by human error or on purpose – to directly connect a USB drive or plug in a USB drive to a computer.
Externally, modern KVM systems allow an organization to achieve “network separation.” With different security classifications of the networks (one being dedicated networks where all the critical processes run and a separate network that may even have access to the public internet, which would make it more at-risk of an external attack), the risk of cyberattacks can be minimized. KVM systems provide the basis for flexible system access and help to harmonize computer technology across systems.
With KVM, users only access the computer interfaces. Several systems are accessible at the same time, but without a data connection between the systems. Organizations can separate critical internal applications in the data flow from external applications like web surfing or external video conferencing. For example, they can keep the critical processes on the internal network and everything that is connected to the outside world can be kept separate.
6. Where is KVM technology likely to go next? What might the next wave of KVM innovation look like?
There is still plenty of improvements to KVM to be made, most of which to accommodate additional size and scope of projects based on the need. More and more, we are seeing increased demand for higher bandwidth, particularly in connection with IP installations, and broader dimensioning of uplinks. Essentially, it’s going to be better quality video, greater scaling, more robust performance, and even more intuitiveness, both for the user and the installer.
As process automation calls for even more interoperability, it will mean the further convergence of informational technology and operational technology (IT and OT). With this, systems will need to have open interfaces to enable the seamless interaction with a video wall or operating systems and devices. Switching commands will be executed remotely.
About Don Hosmer
Don Hosmer, VP Sales Americas & General Manager G&D North America Inc., has more than 30 years of experience in video, audio and data transport applications. He has extensive expertise in control rooms and application design for KVM extension products, switching systems and compression technologies over both copper and fiber cabling infrastructures.
The content & opinions in this article are the author’s and do not necessarily represent the views of ManufacturingTomorrow
Featured Product

